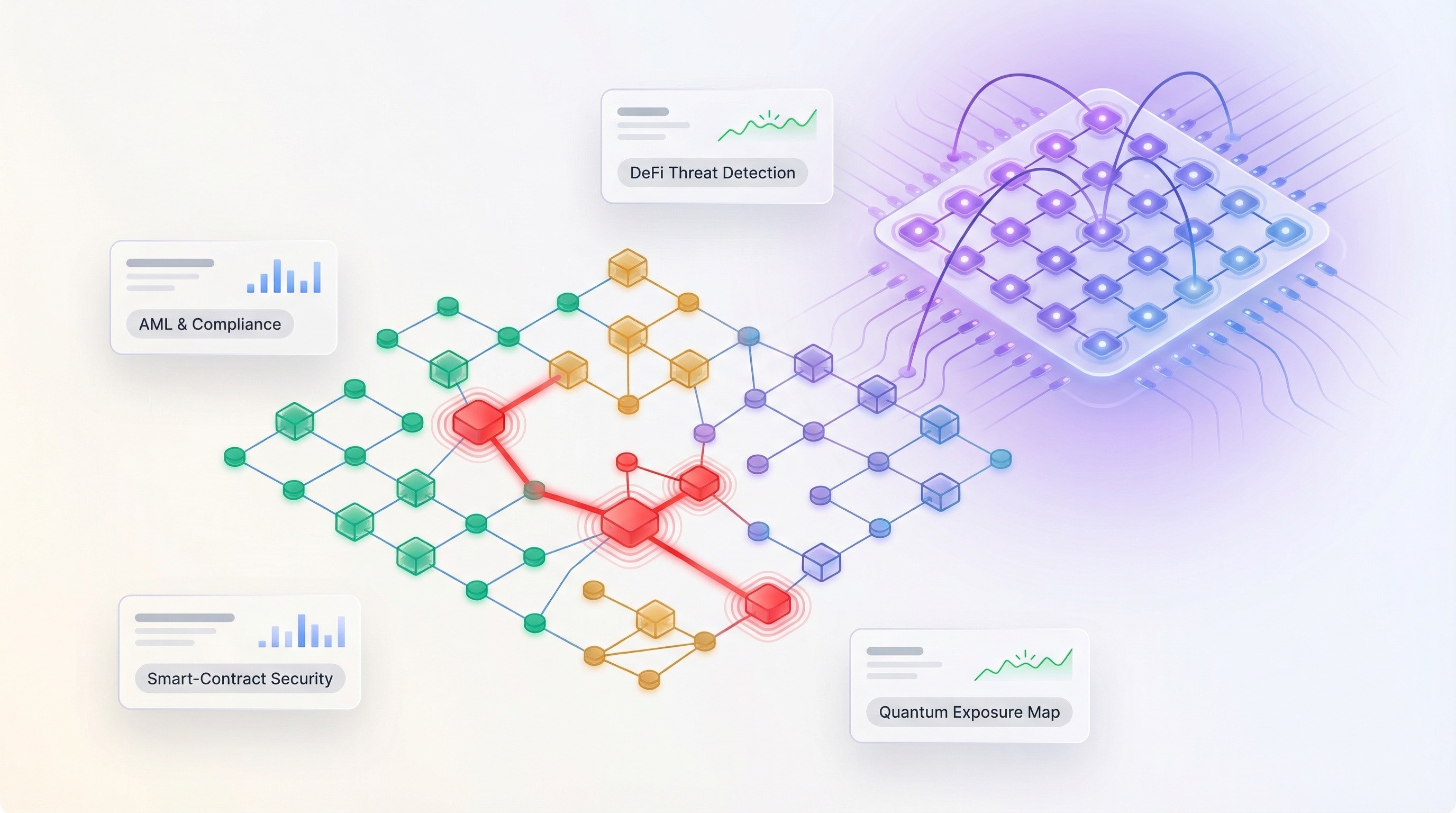
Crypto doesn’t sleep, but the people who guard it still need a fighting chance. In 2025, exchanges and DeFi protocols lost billions to scams, flash-loan exploits and key theft. A sharper threat looms: quantum computers designed to shred today’s cryptography. Researchers estimate 6.3 million bitcoin—about US $648 billion—sit in addresses already vulnerable to a future quantum attack. Risk teams now need tools that flag dirty coins in real time, audit smart-contract land mines and chart every place ECDSA still lurks before it fractures. This guide ranks the ten platforms that do that best and details the scoring model behind each pick.
How we scored the field
We started with a wide net, reviewing “best-of” lists, vendor white papers and Reddit threads. That work surfaced fifteen serious candidates, from household names such as Chainalysis to newcomers chasing quantum bugs.
We then applied one rule: a great risk tool must excel today and stay useful tomorrow. Each platform was scored against six qualities that matter to every compliance officer or security lead:

- Coverage: how many chains and tokens the tool sees
- Threat detection: the logic behind the dashboard, from clustering to machine learning
- Regulatory muscle: built-in workflows for sanctions, the Travel Rule and audit trails
- Quantum readiness: evidence of a practical plan, not claims
- Integration and ease: APIs that slide into real-time pipelines without a half-year sprint
- Cost clarity: pricing that respects startups, enterprises and everyone between
Scores roll up to a 100-point scale. The ten platforms in the next section ranked highest because the numbers say they protect your business best.
With the yardstick set, here’s how they performed.
Take quantum readiness, one of the six pillars: Project 11 ranked near the ceiling because it inventories every ECDSA wallet on a chain and links each address to a post-quantum key with a zero-knowledge proof.
Engineering notes on the firm’s blog add that EdDSA networks such as Solana and Near can flip to quantum-safe signatures without moving funds, while most ECDSA wallets still need a full rotation—another nuance our scoring model rewarded.
At a glance: the top 10 on one page
Before we cover each platform in depth, use this quick reference to match a tool to your biggest pain point.
| Tool | Primary focus | Snapshot of chain coverage | Stand-out feature | Quantum ready? | Best fit for |
| Project Eleven | Post-quantum risk | BTC, ETH plus protocol audits | Maps every ECDSA weak spot and plots a migration path | ? | L1 teams, security architects |
| Chainalysis KYT | AML and investigations | 100+ chains and tokens | Largest attribution database; real-time risk scores | ? | Global exchanges, regulators |
| Elliptic Navigator | AML and compliance | Assets covering 97 percent of trading volume (coverage details) | Fine-grained risk rules tuned for EU, US, APAC | ? | Banks and fintechs expanding coin support |
| TRM Labs | AML and fraud intel | Major L1s, L2s, bridges | Sub-second API for block/allow decisions | ? | High-volume retail exchanges |
| CipherTrace | AML and Travel Rule | 800+ coins, 2,000 entities | Traveler module automates Travel Rule data swap | ? | Banks adding crypto flows to card rails |
| Merkle Science | Predictive AML | Top 20 chains, NFTs | Machine-learning engine that flags mixer-like behavior early | ? | Mid-sized exchanges seeking lower TCO |
| Scorechain | EU-centric compliance | Core coins plus ERC-20 | Drag-and-drop Risk Matrix for audit-ready reports | ? | Regional VASPs under MiCA |
| BlockSec Phalcon | Real-time threat stop | ETH, BSC, major DeFi | Mempool alert that can pause hacks mid-flight | ? | DEXs and bridges on the front line |
| CertiK Skynet | Smart-contract security | Hundreds of audited contracts | Continuous code-health score with exploit alerts | ? | DeFi projects and token-listing desks |
| Crystal Blockchain | Investigations | BTC, ETH, BCH, LTC, Dash | Visual path tracing that wins court cases | ? | Law-enforcement and forensic consultants |
Two quick takeaways:
- Only one tool addresses the quantum gap head-on.
- No single suite covers every risk class, so many teams pair an AML engine with a security monitor.
Keep these points in mind as we explore each platform’s details next.
1 Project Eleven – your early-warning system for Q-Day
Picture a fire drill for cryptography, sparked by Project Eleven’s finding that roughly 6.2 million BTC already sit in addresses whose public keys are exposed to harvest-now-decrypt-later attacks. That is what Project 11 post quantum cryptography runs for every chain it touches.
The platform crawls public keys, node configs and custodial cold-storage setups, flagging every spot where current-gen algorithms stay exposed. A heat-map report marks green for safe, yellow when a key-rotation plan exists and bright red where billions could disappear once quantum computers reach break point.
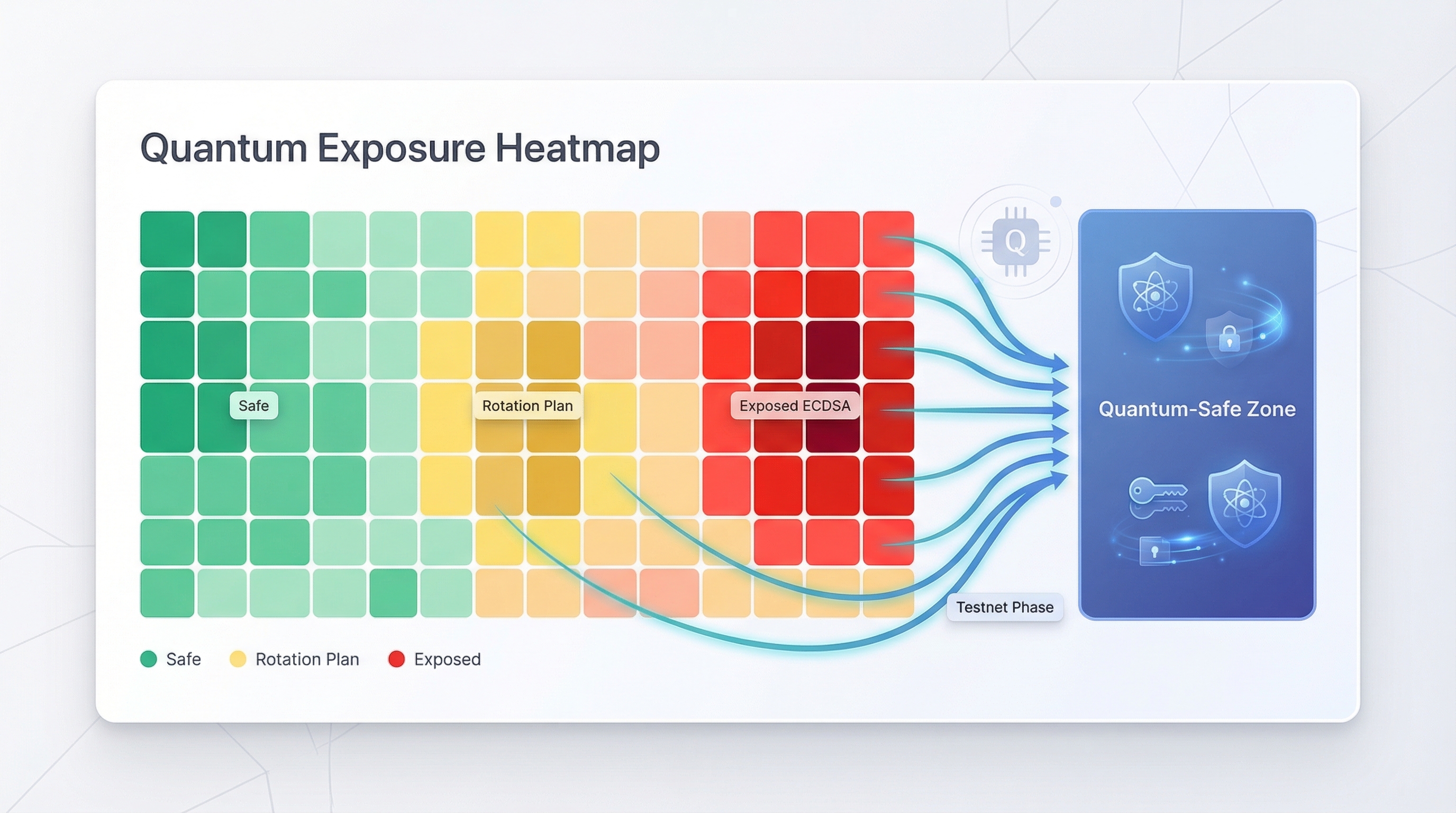
Scope and timing set it apart from a standard audit. Project Eleven links each weakness to a migration sequence (testnet, canary release, full cut-over) so teams can budget and ship fixes before regulators step in. Think of it as DevSecOps for cryptography, bundled with board-ready risk numbers that finally put quantum on the roadmap.
Project Eleven post-quantum risk assessment platform homepage screenshot.
Ideal users include layer-one foundations, custody providers and any exchange that still holds legacy wallets. Pair it with your daily AML tool to handle tomorrow’s existential threat while today’s alerts keep humming.
2 Chainalysis – the compliance workhorse you see quoted in court
Chainalysis is the platform regulators cite when they explain how they traced ransom money. That reputation comes from the company’s deep attribution database, built over nearly a decade of scraping blockchains, darknet forums and seized exchange records.
Open the KYT dashboard and each inbound deposit lights up green, amber or bright red within seconds. Behind the traffic-light view sits clustering logic that links addresses to real-world entities. Tap a red deposit and Reactor expands a clean graph that shows hops through mixers, bridges and dormant wallets until you reach the original hack.
Chainalysis KYT real-time crypto compliance dashboard screenshot.
Coverage matches the market: Bitcoin, Ethereum, ERC-20s, Solana, Avalanche and dozens more. Their data team often adds a new chain within weeks of the first public exploit.
Chainalysis commands premium pricing, but large exchanges pay without blinking because the alternative—a missed sanctioned wallet—can trigger million-dollar fines. Add investigator training, case-management exports and on-prem installs for banks that avoid SaaS, and it is clear why this tool tops most short lists.
Pair Chainalysis with a real-time security monitor to stop risky funds before they leave, then prove where they tried to go.
3 Elliptic – broad coverage, fine-tuned risk rules
Elliptic’s core strength is reach: its Navigator suite tracks assets that account for 97 percent of global crypto trading volume. That reach matters when your exchange lists a fresh alt-L2 or a customer deposits a privacy coin wrapped in a bridge token. Elliptic already sees the traffic.
Open the dashboard and set granular thresholds in seconds. Need darknet exposure over five hops to trigger “high” while gambling services sit at “medium”? Drag two sliders and move on. Compliance teams in Europe value that flexibility because it mirrors how regulators document risk appetite.
Elliptic also stands out culturally. While some rivals spotlight law-enforcement wins, Elliptic courts banks and fintechs stepping into crypto. The UI feels like a treasury platform, and the company’s typology reports help you brief the board without raising alarms.
Pricing sits in the enterprise bracket, though mid-market platforms often negotiate starter tiers. If you want deep asset coverage and reports that pass an audit, Elliptic deserves a close look.
4 TRM Labs – high-velocity API for exchanges that move fast
TRM treats compliance like a performance problem. Each query targets sub-second latency, letting a retail exchange block a tainted deposit before the customer even reloads the screen.
The platform is API-first. Point your transaction stream at TRM, define policy thresholds in JSON and let the engine auto-label each address as funds flow in. When an alert fires, webhooks push a ticket to your case system without manual clicks. That feedback loop saves operations teams hours once spent on spreadsheet triage.
Coverage evolves with the market. If a new bridge or roll-up appears on Friday, TRM’s release notes often show support by the next week. Clear pricing tiers—no “call us” gates—win fans among budget-watching startups.
For builders who value developer time as much as regulator trust, TRM drops into the stack and scales with volume spikes. Pair it with a deeper investigative tool if you need courtroom-ready graphs; for daily screening, few platforms match its speed.
5 CipherTrace – Travel-Rule automation backed by a card-network giant
When Mastercard bought CipherTrace, it signaled that banks expect the same clarity on crypto flows they enjoy on card rails. CipherTrace supplies that clarity.
The Traveler module swaps sender and receiver data between virtual-asset service providers behind the scenes. Your compliance team avoids long email threads, regulators get a clean audit trail and customers move funds without friction.
Beyond the Travel Rule, CipherTrace screens more than 800 coins and 2,000 entities. That reach proves handy when an obscure memecoin surges and bad actors rush in. Visual tracing feels familiar if you know Chainalysis, yet CipherTrace pairs each hop with narrative text you can paste into a SAR.
Pricing varies, and Mastercard’s distribution reach often opens enterprise deals that fold crypto risk into existing fraud budgets. If your business already clears cards, adding CipherTrace feels less like a vendor overhaul and more like turning on an extra data feed.
For institutions straddling legacy finance and Web3, this tool stitches both worlds together without rewriting the playbook.
6 Merkle Science – predictive analytics that surface threats before blacklists
Most AML tools act after the damage. Merkle Science takes a forward stance. Its machine-learning engine studies behavior patterns and flags wallets that behave like mixers or scams weeks before regulators publish a list.
The interface is straightforward. Compliance officers adjust on-screen toggles to set policy, and the system stacks alerts by novelty and risk so small teams focus on the few events that matter rather than a flood of yellow flags.
Built in Singapore, Merkle Science understands lean operations. Pricing tiers start below the legacy giants, and support tickets receive engineer-level answers instead of canned replies.
The trade-off is a smaller historical dataset than Chainalysis, yet for exchanges that value cost control and tomorrow’s typologies today, Merkle Science delivers.
7 Scorechain – Europe-friendly compliance with drag-and-drop controls
Scorechain reads like it was designed by former regulators tired of clunky spreadsheets. Open the Risk Matrix and drag sliders to match MiCA or FATF thresholds, then export a PDF an auditor can approve at first glance.
Coverage centers on the coins most European VASPs handle: BTC, ETH, XRP and common ERC-20 tokens. The tighter scope trims cost and keeps the interface fast. When customers explore a new DeFi asset, Scorechain often adds support within weeks instead of quarters.
Small compliance teams rely on guided workflows; case tickets, Travel Rule fields and SAR templates live in one pane, so nothing falls through email gaps. Larger banks value the on-prem option that keeps wallet data inside their own firewalls.
If you need enterprise polish without a six-figure quote and your regulator’s letters carry an EU postmark, Scorechain delivers.
8 BlockSec Phalcon – real-time mempool defense for DeFi front lines
Most AML tools watch only confirmed blocks. BlockSec studies the mempool, the busy lobby where transactions wait to be mined. That head start lets Phalcon catch exploit signatures such as flash-loan loops or sudden privilege changes while an attacker’s transaction is still pending.
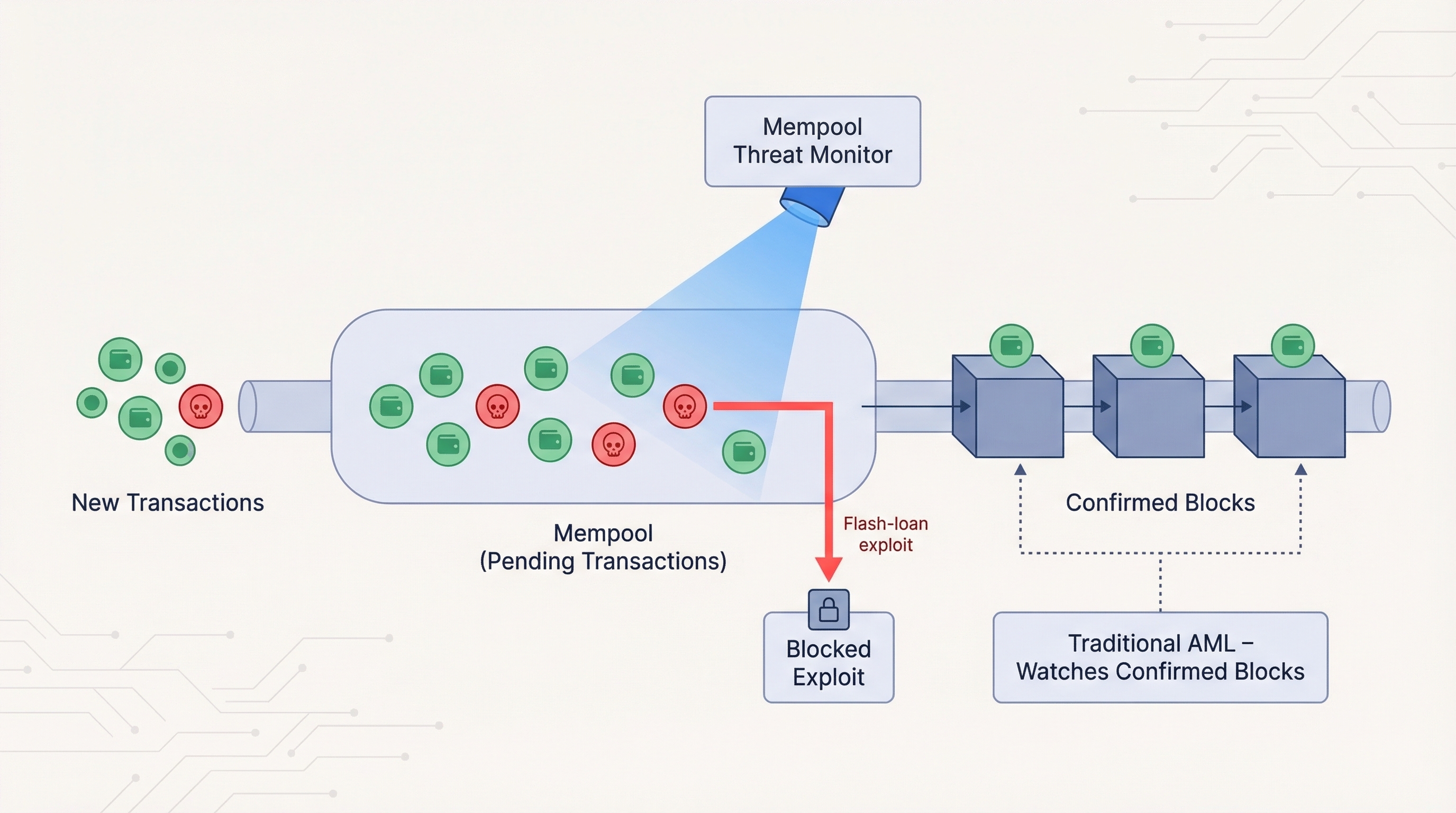
In 2025 the system stopped stolen USDT within seconds of a bridge hack, saving an exchange millions, according to BlockSec.
The dashboard groups threats by tactic: re-entrancy, sandwich, mixer funnel. Security and compliance teams share one vocabulary. Pricing follows a pay-as-you-grow curve; a startup can watch a few contracts for a modest fee, then scale to full exchange coverage later.
Phalcon will not replace a deep attribution database, yet if you run a DEX or bridge and worry about waking up to an empty treasury, it is the safeguard to wire in today.
9 CertiK Skynet – continuous code health for smart-contract listings
Audits freeze code in time, but DeFi keeps moving. CertiK Skynet watches from the moment a project goes live, scoring every contract for logic flaws, privilege changes and governance surprises.
Exchanges value the quick signal. A token’s Skynet score sits beside its price feed, warning listing committees if a pause function sneaks into an upgrade or if whale wallets concentrate too fast. Investors gain the same peace of mind before entering a farm that launched yesterday.
For builders, Skynet works like an automated QA teammate. Dashboards flag re-entrancy risks, out-of-gas paths and admin-key activity so developers can patch issues before social media notices. Alerts flow to Slack or PagerDuty, turning smart-contract risk into a normal DevOps ticket.
Skynet does not handle AML or sanctions, yet when paired with a transaction monitor you cover both sides of the risk coin: the money and the code that moves it.
10 Crystal Blockchain – forensics visualized, cases closed
Crystal turns transaction graphs into images even non-technical juries can follow. Paste an address, press Enter and watch a color-coded map display every hop between victim, mixer and cash-out exchange. Investigators drag nodes, add notes and export a clean PDF that prosecutors can carry into court.
Crystal Blockchain investigation graph interface screenshot.
The engine tags entities with data from Bitfury’s years of blockchain crawling, so labels read “Huobi deposit” or “Conti ransomware wallet” instead of raw hashes. Risk scores refresh as funds move, allowing compliance teams to see an address clean up its record, or fall back into bad habits.
On-prem deployment appeals to law-enforcement groups that treat data sovereignty as non-negotiable. Exchanges often keep Chainalysis for automated screening, then launch Crystal when a high-value case needs narrative clarity.
If your work ends when the bad actors stand trial, Crystal gives you the visual story the other tools never attempt to tell.
Conclusion
Each of these ten platforms targets a different slice of blockchain risk—from AML compliance and real-time threat defense to the looming quantum challenge. Combining complementary tools gives security and compliance teams the coverage they need both now and in the post-quantum future.

