Analysts at Goldman Sachs have raised their year-end 2026 target for the S&P 500 to 8,000 from 7,600, becoming the latest major Wall Street firm to argue that the artificial intelligence investment boom is strong enough to keep driving U.S. equities higher despite mounting geopolitical and inflation risks.
The new forecast implies another 6.4% upside from the index’s latest close of 7,519.12 and supports the increasingly dominant view among large banks that corporate earnings, rather than monetary easing, are now the primary engine behind the market rally.
“Earnings growth has powered the entire S&P 500 return so far this year, and we expect this dynamic to continue in the coming months,” Goldman analysts wrote in a note Tuesday.
The bank also sharply increased its earnings projections for U.S. companies, forecasting S&P 500 earnings per share of $340 in 2026, representing roughly 24% annual growth, followed by another 13% increase to $385 in 2027.
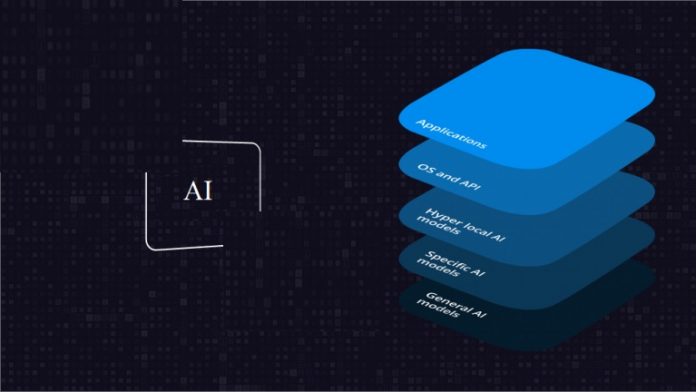
The upgraded outlook highlights how rapidly Wall Street expectations have shifted around artificial intelligence and its impact on corporate profitability. Only months ago, investors were focused primarily on recession risks, elevated interest rates, and geopolitical instability stemming from the war involving the United States, Israel, and Iran. Now, many strategists increasingly believe the scale of AI-related spending is large enough to offset broader economic weakness.
Goldman said companies tied directly to AI infrastructure, particularly semiconductor firms and data center suppliers, are expected to generate roughly half of the S&P 500’s total earnings growth this year.
That reflects the extraordinary concentration now shaping U.S. equity markets.
A relatively small group of AI-linked companies, including major chipmakers, hyperscalers, and cloud infrastructure providers, has increasingly become responsible for a disproportionate share of market gains. Massive capital expenditures by technology giants on AI servers, chips, networking equipment, and energy infrastructure continue flowing through supply chains at a pace analysts say remains historically unusual.
The bank noted that semiconductor stocks “at the heart of the AI infrastructure complex” have recently been outperforming even their already rapidly rising forward earnings estimates. That observation significantly suggests investors are not simply rewarding current profits, but are increasingly pricing in expectations that AI spending could continue accelerating for years.
The optimism comes as corporate America embarks on one of the largest infrastructure buildouts in decades. Companies including Nvidia, Advanced Micro Devices, Microsoft, Amazon, and Alphabet are collectively spending hundreds of billions of dollars on AI computing infrastructure, data centers, and custom chips.
That investment wave has extended far beyond Silicon Valley, boosting demand for energy producers, utilities, networking firms, server manufacturers, memory-chip makers, and industrial suppliers.
Goldman’s call adds to a broader pattern of increasingly bullish forecasts from Wall Street firms. Last week, UBS also raised its market outlook, arguing that AI-related earnings growth could help absorb the impact of stubborn inflation, supply-chain disruptions, and elevated oil prices tied to the Iran conflict.
The bullishness persists even as several macroeconomic risks continue building beneath the surface. Oil prices remain far above pre-war levels due to disruptions around the Strait of Hormuz, keeping pressure on transportation, manufacturing, and consumer costs globally. Inflation concerns have also altered expectations for Federal Reserve policy, with traders recently increasing bets that the central bank may still raise interest rates again rather than cut them.
At the same time, economists continue warning that the broader U.S. economy outside the technology sector appears considerably weaker than headline market indexes suggest. Consumer spending growth has slowed, borrowing costs remain elevated, and several sectors tied to housing, retail, and manufacturing continue showing signs of strain. Market gains have also become increasingly concentrated among large-cap technology and AI-related stocks, raising concerns about valuation risk.
Goldman acknowledged some of those vulnerabilities, noting that weak consumer demand and higher operating costs still pose threats to earnings growth. Yet the bank argued that the scale of AI investment is currently overwhelming those concerns.
The revised forecasts suggest Wall Street increasingly views AI not simply as another technology trend, but as a structural economic transformation capable of sustaining corporate profit growth even during periods of geopolitical instability and tighter monetary policy.
That belief has become the defining force behind the current bull market. Investors are effectively betting that the race to dominate artificial intelligence infrastructure will continue generating enough revenue, productivity gains, and capital spending to support U.S. equities well into the end of the decade.