1. Executive Summary
In the wake of recent cyber attacks launched against nations through malicious codes like Stuxnet, Duqu and Flame, and in response to the formalization of cyber-crime legislation in Nigeria’s parliament, it has become imperative for our nation to establish an operations centre to address the rising incidence of cybersecurity and cyber attacks. In Nigeria, many government websites have been consistently defaced and thefts of strategic digital assets – commercial and governments secrets – might have occurred. If the nation cannot mitigate the threats of evolving Information Warfare (IW) which uses digital technology in pursuit of a competitive advantage over nations, our long-term economic blueprint could be compromised.
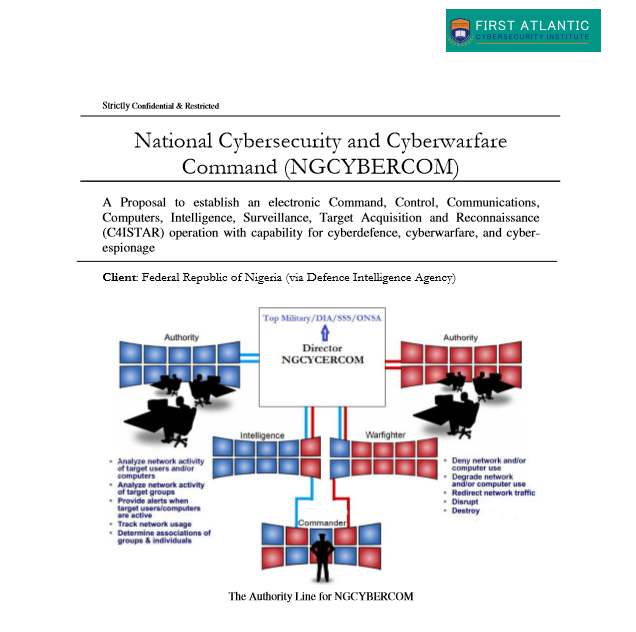
This center can be structured as an electronics Command, Control, Communications, Computers, Intelligence, Surveillance, Target Acquisition and Reconnaissance (C4ISTAR) operation and tasked with ensuring the protection of highly secured data and information against cyber attacks. It can also wage cyber warfare for the nation where necessary.
Register for Tekedia Mini-MBA edition 20 (June 8 – Sept 5, 2026).
Register for Tekedia AI in Business Masterclass.
Join Tekedia Capital Syndicate and co-invest in great global startups.
Register for Tekedia AI Lab.
Across the globe, there is a new war evolving in the world. It is not fought on the land, sea, air or even in the physical space. It is war of the fifth domain: the cyberspace. Yes, warfare perpetrated through clusters of computer networks which have linked the world in mutually dependent interrelationships of people, firms and nations.
Cyberwar is not a war of choice. It will come to Nigeria even if the nation does not want it. Just as computer virus attacks computers, this warfare is waged at national level with consequences that can shut down a military control, financial systems, health informatics, and telecommunication networks. It is something that the nation cannot afford to waste time despite our failure to use technology or strong regulation to solve the embarrassment caused by the Nigerian web fraudsters.
The world has nuclear non- proliferation treaty, but none exists for cyberwar despite the potential economic dangers the latter poses to world commerce. Accordingly, many nations have started to deploy strategic commands to protect, defend and necessarily retaliate when their systems are attacked through cyber-means. The United States Pentagon has the Cyber Command inside the National Security Agency, the British has a similar unit inside the GCHQ. China, Iran, Russia, Israel, and many other nations have developed cyber-army to protect their economies.
What is basically the threat of a cyberwar? It has been proven that people could remotely rewire networks logically and trigger avalanche of problems that can bring a nation’s economy to standstill. They plant logic bombs which on ‘explosion’ brings enormous damages to companies and private citizens. They could penetrate our oil installations, bank servers, electric grids, air-traffic controls, GSM networks, and military commands. We suddenly find out that nothing works in the land and all networks are broken.
This is perhaps the most drawbacks of computer networks- the ability to wage war through bits and bytes instead of the old fashioned way of firing bullets where the identities of the invaders are known. In cyberwar, the attackers could mask themselves and may even use your rigged networks to attack you. It is also important to understand that the world ‘computer’ has since evolved. There are pills, watches, shoes, bags, cellphones that are indeed computers. And most systems are on networks with IPs assigned to them.
In the old warfare, people were trained to become spies or soldiers with enormous risks. But now, all they have to do is use a computer to launch their strikes to vulnerable nations. If we deny the severity of these threats, we will have ourselves to blame. It used to be copies of military notes; now, the digital spies could download an entire library of military strategy.
The cyberwar is real and it is already taking place in the world. The first Web War 1 was fought in Estonia where series of orchestrated attacks on Estonian digital infrastructure forced the government to decouple the nation from Internet. In other words, both government and business websites were brought down. That was followed in Georgia during its brief recent hostility with Russia. Again, its websites were brought down and even the President website had to be moved to a secure server.
It is important to understand that this is not an ICT problem. This is a serious engineering problem that requires the use of advanced mathematical models and analytics in digital offense and defence.
First Atlantic Cybersecurity Institute proposes to assist the nation design, develop and implement a national cybersecurity, cyberdefence and cyberwarfare command. It is projected to transform the nation with capability to survive the data wars of the 21st century with cyber experts that can use analytics to connect dots and identify security patterns via automated data sharing in volume, variety and velocity.
As part of this proposal, a whitepaper is prepared for the Nigerian Military to assist in developing a world-class National Cybersecurity and Cyberwarfare Command modeled after the United States National Security Agency.
For the complete Whitepaper, email First Atlantic Cybersecurity Institute.



