West African cybercriminals have one skill they are particularly good at—defrauding victims. But why resort to cybercrime? It is actually quite simple, almost half of the 10 million graduates from more than 668 African universities each year do not find employment. According to the INTERPOL survey, West African law enforcement agencies recognize that about 50% of the cybercriminals that they identified in the region are unemployed.
Trend Micro Incorporated, a global leader in cybersecurity solutions, in collaboration with INTERPOL, has released research on cybercriminal activity in West Africa, “Cybercrime in West Africa: Poised for an Underground Economy,” as part of its ongoing Cybercriminal Underground Economy Series (CUES).
A Kenyan firm released one few days with specific focus on Nigeria where it put the total cyber-crime related losses for Africa at $2 billion with Nigeria contributing more than 25%.
Register for Tekedia Mini-MBA edition 20 (June 8 – Sept 5, 2026).
Register for Tekedia AI in Business Masterclass.
Join Tekedia Capital Syndicate and co-invest in great global startups.
Register for Tekedia AI Lab.
Trend Micro – INTERPOL Research
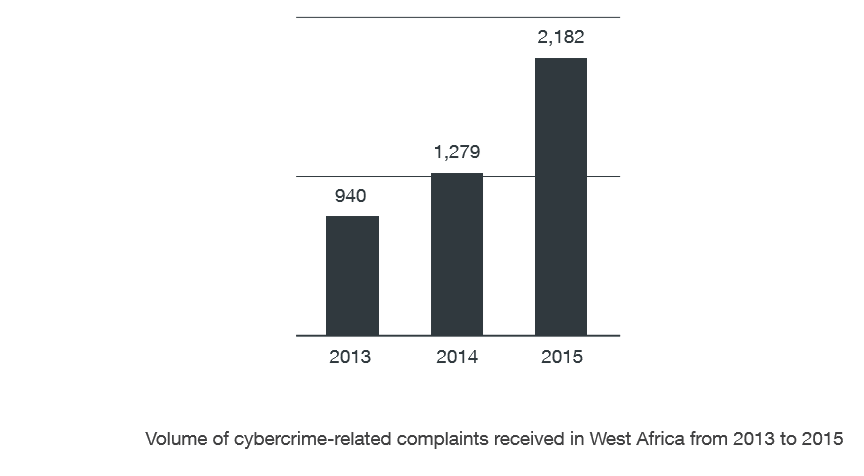
Trend Micro research showed that scams targeting individuals and businesses have grown exponentially since 2013.The research revealed that West African cybercriminal activity is driven by two types of threat actors: Yahoo Boys and Next-Level Cybercriminals.
Yahoo Boys, named for their reliance on Yahoo apps to communicate, became the primary type of cybercriminal in this region in the early 2000s. They focus on less technically advanced schemes, including advanced-fee, stranded traveler and romance scams under the supervision of a ringleader.
Next-Level Cybercriminals are able to execute more sophisticated attacks, such as Business Email Compromise (BEC) and tax scams. The more complex attacks take more time and investment, but the average BEC scam results in a payout of $140,000, making it worth the extra time and effort.
They use malware (keyloggers, remote access tools/Trojans [RATs], etc.) and other crime-enabling software (email-automation and phishing tools, crypters, etc.) that are easily obtainable from underground markets.
One constant finding throughout Trend Micro’s CUES research is that each underground marketplace culturally reflects the region in which it operates, and West Africa is no exception. Cybercriminals here openly communicate, even potentially meeting in person, sharing best practices and encouraging newcomers. This has developed a culture among threat actors that encourages scamming and supporting one another.
Partnership Required
This report further highlights the importance of public-private partnerships in identifying and arresting cybercriminals, as well as educating businesses and governments about cyber threats. Trend Micro and INTERPOL have a longstanding partnership, with joint operations and research leading to the takedown of cybercriminal networks in a collective effort to make the digital world safer for everyone.
One such collaboration in 2016 resulted in the arrest of a Nigerian national who had extorted $60 million from businesses around the world using BEC scams
Evolving Underground Market
Cybercriminals are bound to continue honing their know-how, skill sets, and arsenals to slowly but surely form their own community. There may not be a West African cybercriminal underground market now, but cybercrime is definitely an issue in the region. This can be seen from the constant increase in the volume of cybercrime-related complaints targeting both individuals and businesses that law enforcement agencies in the region receive, as shown by the INTERPOL survey.
These are many companies of this evolving market which must be curtailed:
- Yahoo Boys
Yahoo boys, dubbed such due to their heavy use of Yahoo!® apps for communication via email and instant messaging (IM) in the early 2000s, are often part of groups operating in the same physical location— normally cybercafés. They are supervised by more experienced cybercriminals—usually ringleaders or gang masterminds. Each cybercriminal takes care of an entire operation—from scouring the Internet for email addresses to send spam to, to communicating with each potential victim, and finally receiving the defrauded money. This operating model does not require work segmentation and specialization. Cybercriminals can use more than one fraud type at the same time. In fact, they usually run several different types of fraud at the same time. They can, for instance, run a romance fraud with one victim and an advance-fee fraud with another while sending a stranded-traveler fraud email to other potential victims - Advance-Fee Fraud
The advance-fee fraud12 is the oldest and simplest fraud type. It is also the most varied in terms of pretense and storyline, though the most popular type is the Nigerian prince fraud.
In the Nigerian prince fraud, the cybercriminal asks a target to help transfer large sums of money with the promise of compensation after providing assistance. However, prior to being compensated, the victim is asked to pay small amounts supposedly for various fees—deposits, notarization, parcel, and transfer fees—that in the end, add up to hundreds, even thousands of dollars. - Stranded-Traveler Fraud
Stranded-traveler fraud first gained notoriety in the early 2010s. These used compromised Facebook and other social networking accounts to request money from the account holders’ contacts. In this type of fraud, the cybercriminal first take control of an account then impersonates the account owner and asks contacts for help with an “emergency,” usually while overseas. The supposed emergency can range from incarceration, kidnapping, a sudden health-related case, or being robbed at gunpoint—anything that would require immediate, no-questions-asked monetary assistance. - Romance Fraud
Romance fraud14 typically involves creating fake but very appealing (to as many potential suitors as possible) accounts on several online-dating sites. Romance fraud can be likened to a “long con,” a confidence trick that usually runs for weeks, even months. In it, the cybercriminal spends time building an online relationship with a target.
Communication Tools
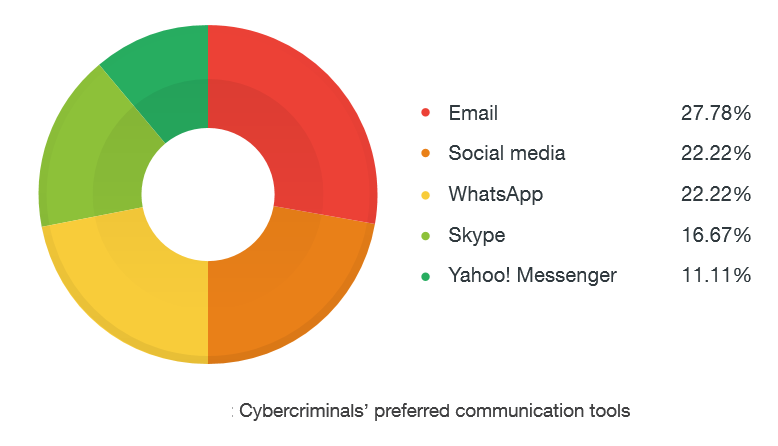
West African cybercriminals typically operate in tight-knit groups. Each group member constantly communicates with peers—sharing targets, compromised email accounts, tools, and best practices. Though cybercriminals use attack tools usually restricted to technical communities or only commonly seen in underground markets, the communication tools they use are less clandestine in nature. According to the INTERPOL survey, most West African cybercriminals use email and social media to communicate with one another although some still use IM applications such as Yahoo! Messenger.
Education and Training
West Africa has to invest in cybersecurity training and awareness. One of the global companies working in the policy, technology and management aspects of cybersecurity and digital forensics covering the region is First Atlantic Cybersecurity Institute. Governments, schools and businesses can take advantage of the training programs provided by Facyber.





[…] more than $400 billion to hackers. Nigeria is losing millions of dollars via cyber-attacks – $550 million in […]
[…] than $400 billion to hackers. Nigeria is losing millions of dollars via cyber-attacks – $550 million in […]