
If you haven’t suffered a cybersecurity breach you’ve either been incredibly well prepared, or very, very lucky. Are you incredibly well prepared?
Whether it’s design plans, medical records or good, old-fashioned payment card details — someone, somewhere will see it as their meal ticket. Most cybercriminals are not fussy about who they steal from.
You could be the next victim of a data breach. And that could impact every part of your business. That’s why everyone in your company — not just the security experts — needs to understand the threats and how to mitigate them.
Register for Tekedia Mini-MBA edition 18 (Sep 15 – Dec 6, 2025) today for early bird discounts. Do annual for access to Blucera.com.
Tekedia AI in Business Masterclass opens registrations.
Join Tekedia Capital Syndicate and co-invest in great global startups.
Register for Tekedia AI Lab: From Technical Design to Deployment.
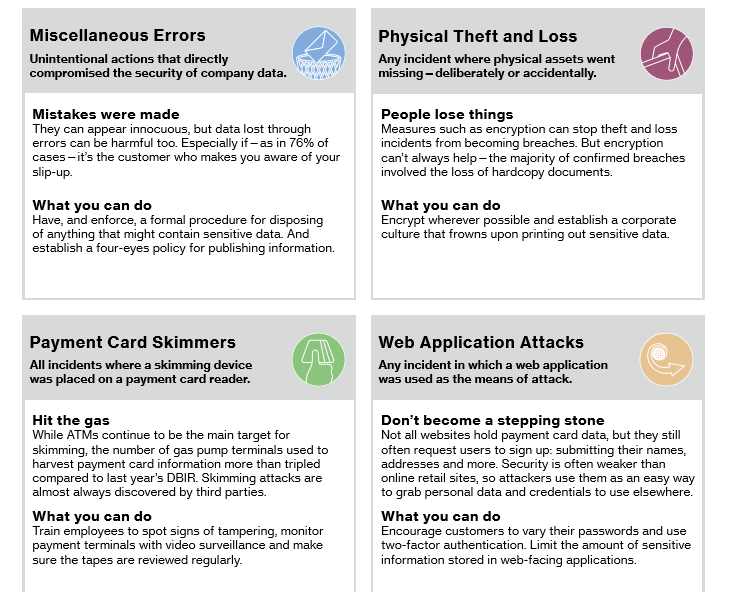
- Cybercrime can come in any shape or size, and not always the form you’d expect
- Each industry faces a distinctive pattern of threats
Verizon released its 10th edition of Data Breach Investigations Report early Thursday morning. Teaming up with 65 contributing organizations, Verizon’s analysts scrutinized 42,068 security incidents, of which 1,935 qualified as full-blown data breaches. They sliced and diced the data every which way.
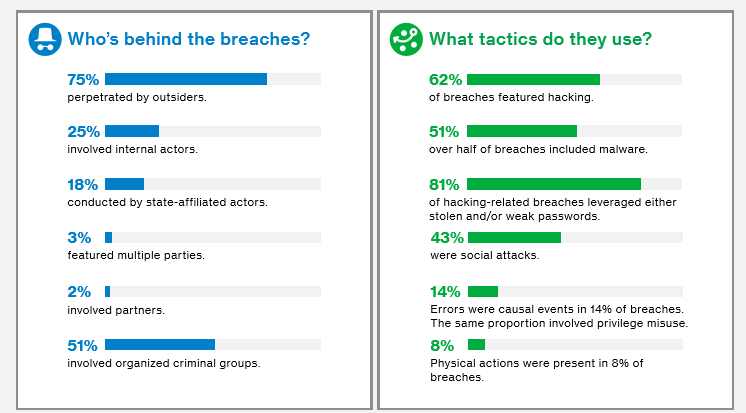
Here are some of the bits: First, each industry has its own flavor. The tech sector is the most reliable at patching its systems, sealing up 97.5% of known holes within 12 weeks of a vendor releasing software updates. (Compare that to retail and to food and hospitality, where little over 60% gets patched in the same time period.) The manufacturing, education, and public sectors are the most rife with cyberespionage, where spies seek to steal intellectual property, proprietary research, and state secrets. Healthcare is the only industry in which insider threats, meaning rogue employees, are the predominant threat actor. And financial services and insurance companies most commonly contend with distributed denial of service attacks, which overload computer servers with Internet traffic.
Another notable finding: ransomware continues to explode. The frequency of attacks featuring this malicious software, which holds victims’ computer files for ransom, increased 50% in 2016 compared to the year prior. This year ransomware clocked in as one of the top five most common varieties of malware, rocketing from 22nd place in 2014. It’s worth noting that Verizon’s analysts counted ransomware attacks as “incidents” rather than “data breaches” in the report, “because typically we cannot confirm that data confidentiality was violated.” In other words, it’s hard to know whether the attackers actually laid eyes on the data they locked up.
For some Saturday reading, I recommend the full report. No document provides a more rigorous overview of the security challenges businesses face today. In an industry where marketing puff often crowds out reliable information, the Verizon report is a welcome read.


